Cleaning Pasted Configuration Data to Prevent System Errors
Messy configuration data is one of the fastest ways to introduce silent failures into a…
Best Practices for Data Security in Web Apps
Best Practices for Data Security in Web Apps Now that you run a web app,…
How APIs Handle Time Zones and Data Sync
How APIs Handle Time Zones and Data Sync - CFREAKS Opening paragraph: Time is a…
Understanding Unix Epoch Time for Developers
Understanding Unix Epoch Time for Developers If you work with logs, APIs, or any data…
Debugging API Timestamp Errors with a Real Time Clock Reference
API systems depend on time. Authentication tokens expire based on timestamps. Signed URLs rely on…
Unix Epoch Time for Developers and Admins
Time sits quietly under every system you run. Logs rely on it. Databases depend on…
Building Reliable Apps: Time, Time Zones, and API-Based Solutions
Modern applications run across regions, clouds, and devices. Time sits at the center of all…
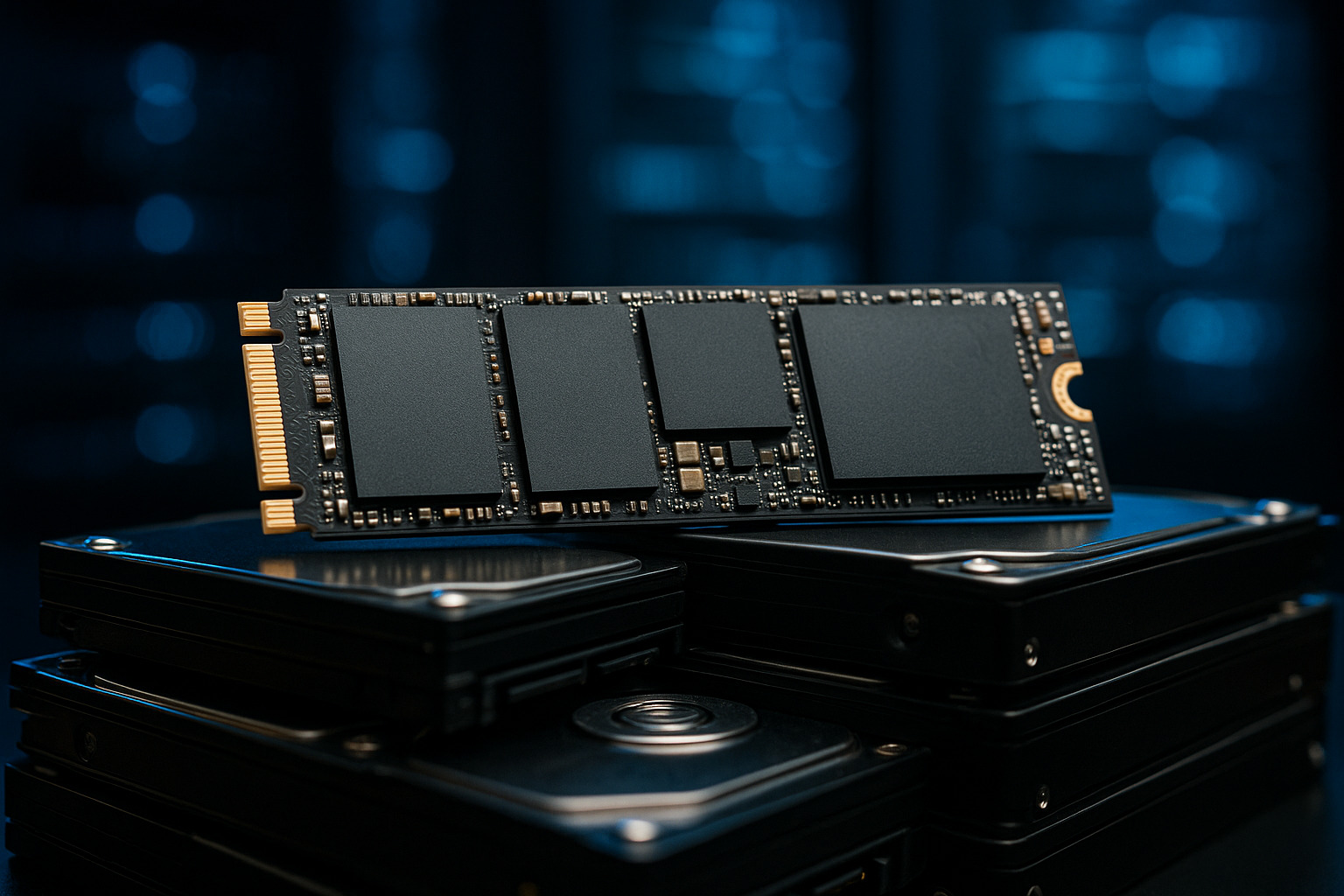
The Future of Solid-State Drives: Predictions for the Next Decade
Solid-state drives (SSDs) have already disrupted how data is stored, transferred, and accessed. As demand…
Building a Budget Gaming PC: Essential Components and Tips
Can you game on a budget without sacrificing performance? Absolutely. Building a gaming PC under…
Comparing the Top Encryption Software Options for Data Protection
Is your data safe enough? Encryption software is your first and strongest line of defense…